Critical IngressNightmare vulnerability affects the Kubernetes Ingress NGINX Controller

Information has been disclosed about IngressNightmare, a set of five new vulnerabilities affecting the Kubernetes Ingress NGINX Controller. IngressNightmare could allow a remote attacker to execute commands without authentication.
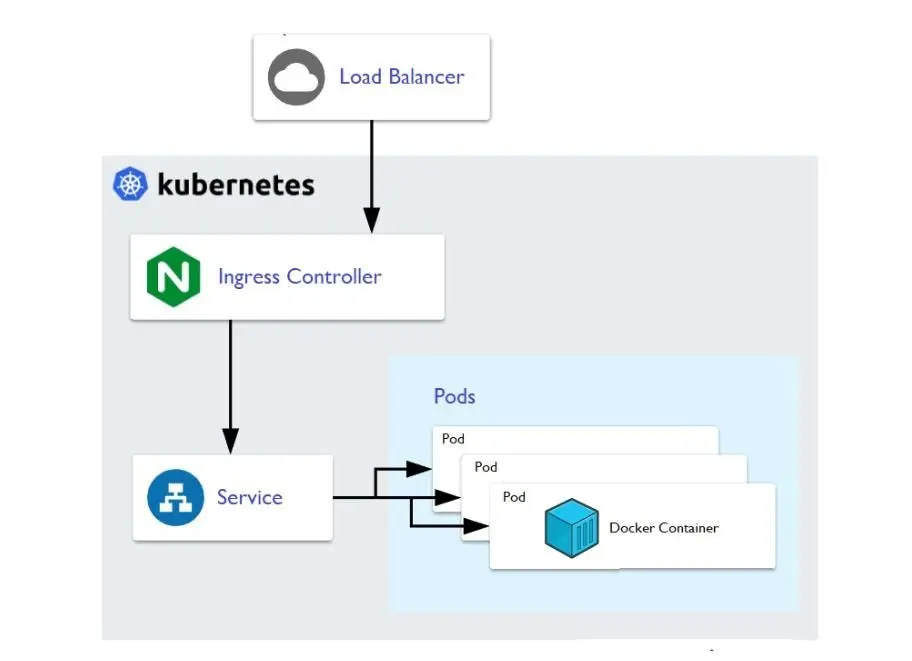
Ingress exposes HTTP and HTTPS routes from outside the cluster to services within it. Traffic routing is controlled by rules defined in the Ingress resource.
The following is a simple example where an Ingress sends all its traffic to a single service:
Main features of IngressNightmare
The main characteristics of the five vulnerabilities collectively known as IngressNightMare are detailed below:
- Vulnerability CVE-2025-1974:
- Affected Software: Ingress Nginx Controller
- CVSS Vector: CVSS:3.1/AV:N/AC:L/PR:N/UI:N/S:U/C:H/I:H/A:H (9.8 Critical)
- Summary: An unauthenticated attacker with access to the pod network can achieve arbitrary code execution in the context of the ingress-nginx controller under certain conditions.
- Public exploit: Yes, see the next link.
- Vulnerability CVE-2025-1098:
- Affected Software: Ingress Nginx Controller
- CVSS Vector: CVSS:3.1/AV:N/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H (8.8 High)
- Summary: The Ingress mirror-target and mirror-host annotations can be used to inject arbitrary configuration into NGINX, resulting in the execution of arbitrary code in the context of the ingress-nginx controller and the disclosure of secrets accessible to the controller.
- Public exploit: Yes.
- Vulnerability CVE-2025-1097:
- Affected Software: Ingress Nginx Controller
- CVSS Vector: CVSS:3.1/AV:N/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H (8.8 High)
- Summary: The auth-tls-match-cn Ingress annotation can be used to inject configuration into NGINX, resulting in the execution of arbitrary code in the context of the ingress-nginx controller and the disclosure of secrets accessible to the controller.
- Public exploit: Yes.
- Vulnerability CVE-2025-24514:
- Affected Software: Ingress Nginx Controller
- CVSS Vector: CVSS:3.1/AV:N/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H (8.8 High)
- Summary: The auth-url Ingress annotation can be used to inject configuration into NGINX, resulting in the execution of arbitrary code in the context of the ingress-nginx controller and the disclosure of secrets accessible to the controller.
- Public exploit: Yes, see the next link.
- Vulnerability CVE-2025-24513:
- Affected Software: Ingress Nginx Controller
- CVSS Vector: CVSS:3.1/AV:N/AC:H/PR:N/UI:N/S:U/C:L/I:N/A:L (4.8 Medium)
- Summary: The ingress-nginx Admission Controller feature includes attacker-supplied data in a filename, causing directory traversal within the container. This could lead to a denial of service or, in combination with other vulnerabilities, limited disclosure of cluster secret objects.
- Public exploit: No
Mitigation
The primary solution is to urgently update the NGINX Ingress controller to the new available versions that address this vulnerability:
On March 24, Kubernetes released a statement with official information and possible updates related to this vulnerability:
| Affected products | Affected versions | Fixed versions |
|---|---|---|
| Ingress NGINX Controller | 1.12.0 | 1.12.1 |
| Ingress NGINX Controller | 1.11.4 & below | 1.11.5 |
To check the installed version of Ingress NGINX Controller, the following command can be executed:
kubectl get deployment -n ingress-nginx -o jsonpath="{.items[
].spec.template.spec.containers[
].image}"
Additionally, it is recommended to:
- Ensure that the admission webhook endpoint is not exposed to the Internet.
- Implement strict network policies to limit access to the admission controller.
- Temporarily disable the admission controller if immediate updates are not possible using: controller.admissionWebhooks.enabled=false for Helm installations.
Finally, customers can use the following command to determine if their clusters are using ingress-nginx:
kubectl get pods --all-namespaces --selector app.kubernetes.io/name=ingress-nginx
As part of its emerging vulnerability service, Tarlogic proactively monitors its clients’ perimeters to urgently report, detect, and notify them of this vulnerability, as well as other critical threats that could seriously impact the security of their assets.